Users are receiving a pop-up asking to "select a certificate to authenticate yourself" when accessing Bitbucket
Platform notice: Server and Data Center only. This article only applies to Atlassian products on the server and data center platforms .
Summary
After upgrading Bitbucket, a few users are receiving a pop-up asking to Select a certificate to authenticate yourself to <Bitbucket server web address>:443. The pop-up appears when the user access the Bitbucket dashboard. User receives window prompt asking for certificate. If a user clicks okay, it results in the page not loading. If the user selects cancel, they are telling the site to not use the certificate as a method of authentication.
Environment
- Bitbucket Server running on Windows
- Any browser is affected. Tested in Chrome, Edge, Firefox
- Using a certificate issuer by MS-Organization-Access
- Customized bitbucket.properties property for server.ssl.client-auth
Diagnosis
- Verify pop-up message received is Select a certificate to authenticate yourself to <Bitbucket server web address>:443.
- Verify custom configuration for the property server.ssl.client-authin file $BITBUCKET_HOME/shared/bitbucket.properties.
- Verify certificate issuer is MS-Organization-Access.
Cause
The certificate issuer MS-Organization-Access comes from Active Directory Federation Services and the certificate is automatically generated when someone uses a federated service such as Azure.
SOLVED: What is MS-Organization-P2P-Access [2021] Certificate?
One of client had Logic Monitor kick off the following ticket:
Eventsource: Windows Exchange EventsWindows
Event ID: 25
Message: The Exchange certificate [Subject] CN=11f90176-4bca-4cec-90fa-2a7bdc7b5181
DC=88467e97-b67a-4906-983f-c201d2100bc8
[Issuer] CN=MS-Organization-P2P-Access [2021]
[Serial Number] 128616464061E8F328FAE2380BB88E82
[Not Before] 7/1/2022 5:46:40 PM
[Not After] 7/2/2022 5:51:40 PM
[Thumbprint] 8E1AA568E95C7BAE26E1BCEB8728E2D43D54DD21 will expire very soon on 7/2/2022 5:51:40 PM.
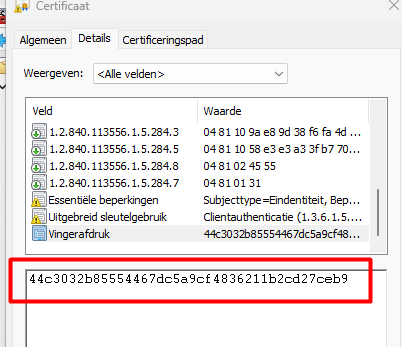
The certificate in question looks like:
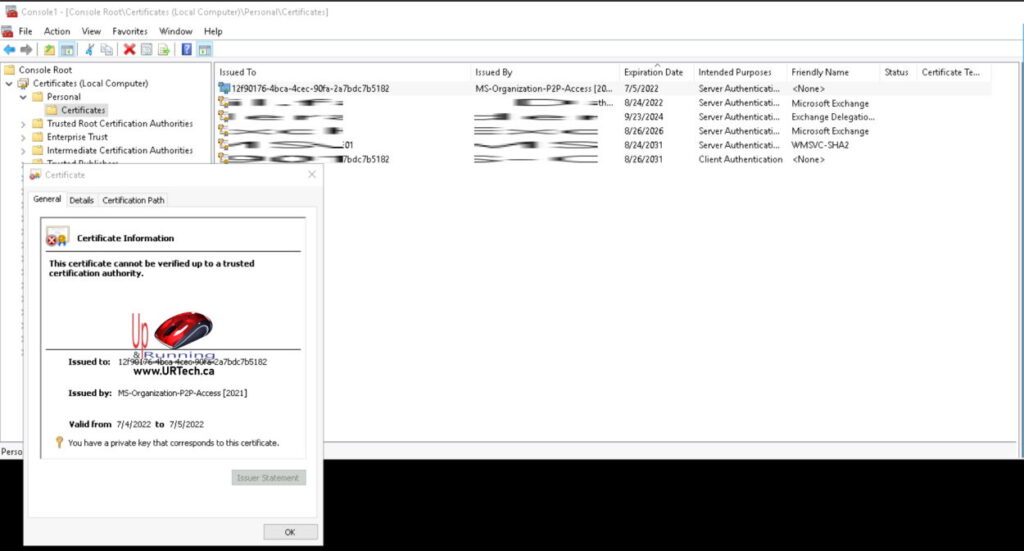
What is a AD Service Principal “P2P Server” Certificate?
A MS-Organization-P2P-Access certificate is:
- valid for only 24 hours
- generated by Azure and issued to an on-premise server
- enables Azure AD credentials to be used in an RDP session
It only has a one day life because the MS-Organization-P2P-Access is not generally needed for longer. You will notice that is starts appearing in Windows logs after AD FS Device Registration has been enabled.
These MS-Organization-P2P-Access certificates are NOT automatically renewed when they expire; they are automatically replaced only when they are needed again.
You can safely ignore them and the fact that they are expiring.
Who Issues MS-Organization-P2P-Access Certificates?
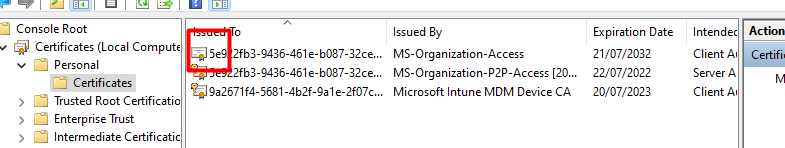
Look in Local Computer\AAD Token Issuer\Certificates and you will see your own on-premise computer issues the MS-Organization-P2P-Access certificates.
The certs are issued to both the user and the computer so they are present in both:
The TenantID from Toronto
After reading a question on Reddit in which was asked how Intune knows which device belongs to which organization I decided to write a dedicated blog about this question.
Hopefully, with this blog, we can get a good understanding of how important the MS-Organization-Access certificate and the Intune MDM device certificate are
I will divide this blog into multiple parts
- Introduction
- Removing the MS-Organization-Access certificate
- Importing the MS-Organization-Access certificate
- OID’s
- Cleaned up Intune Objects
1. Introduction
I already wrote a fair amount of blogs about the MS-Organization-Access certificate. In this blog below, I am explaining how trust is being built between your device and Azure. Please read it before reading the other parts of this blog!
To give you a small summary: It’s all about your TPM, Transport/Device Keys.
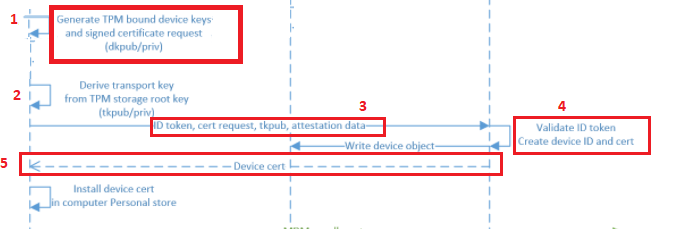
2. Removing the MS-Organization-Access certificate!
To get a better understanding of how important this wonderful MS-Organization-Access certificate is I decided to remove it from a working enrolled device. If you haven’t tried it yourself, just do it! Of course not on your production device… but that’s obvious right?
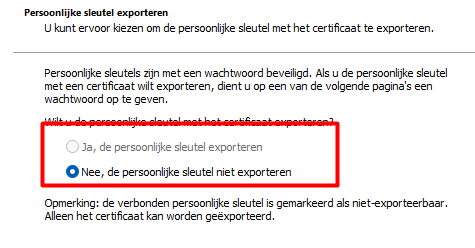
Please note: Before I choose to delete it, I exported it to a .cer file (without the private key… as it’s not exportable of course)
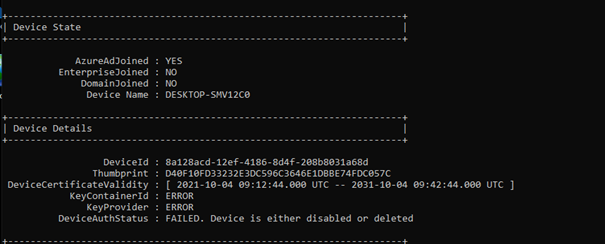
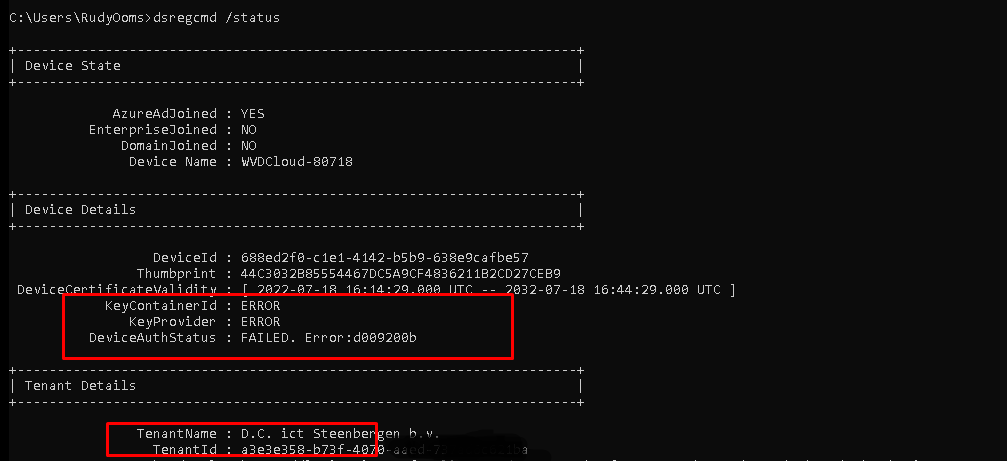
Shall we take a look at the dsregcmd /status output first? The picture below is a screenshot before I deleted the certificate
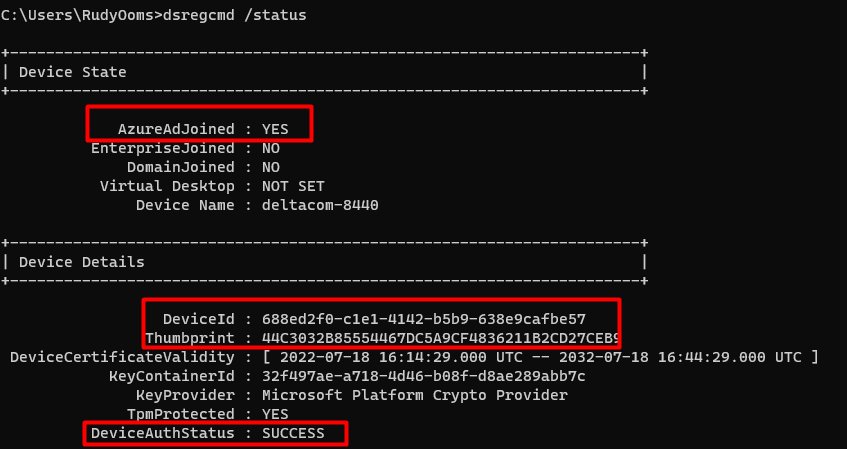
As shown above, DSREGCMD is showing us, the fact that our device is “AzureAdJoined” and it is showing us the Device Details. In these details, we are noticing the “Thumbprint” that matches our MS-Organization-Access certificate and the DeviceAuthStatus is a SUCCESS
After deleting this certificate I rerun the DSREGCMD /status command. This screenshot was taken just 1 second after I deleted the certificate
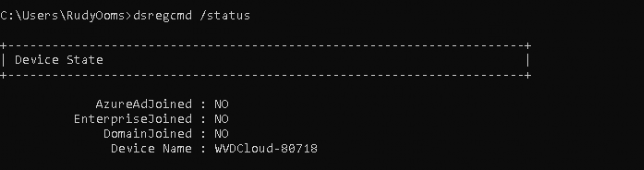
As shown above, when the MS-Organization-Access certificate is removed, your device becomes Azure Ad Unjoined instantly!
As the Device Certificate is responsible for a working Azure Ad Join, it broke immediately. Also rebooting the device ended up in the same issue I showed you earlier. A nice login screen with no possibility to log in with your Azure Ad User!
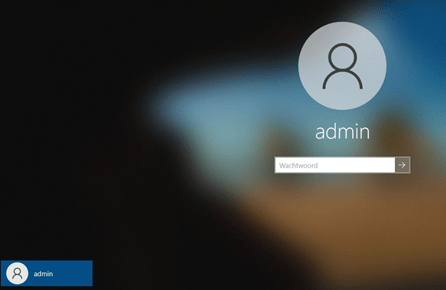
But what happens when we import the old Device Certificate back into the store on that same device? As shown below, as it is missing the private key binding we don’t have the “Key Icon”
Let’s open the CMD again and take a look at what DSREG has to tell us now the cert is back again!
As shown above, the device was immediately Azure Ad joined again. But did you notice the DeviceAuthStatus: Failed. “Device is either disabled or deleted.”
Luckily you could restore the connection with the dsregcmd /forcerecovery option? But why should we when we can use certutil to fix the binding as shown in this blog below?
With the use of the certutil -repairstore command, we can fix the binding again because we still have the private key somewhere. You can find it out yourself by running this PowerShell command
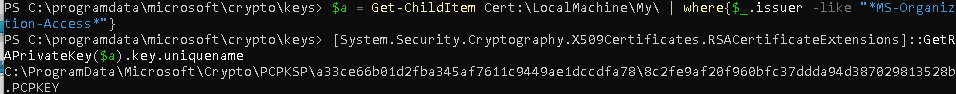
As shown above, the PowerShell command is giving us the exact location where we need to look
C:\ProgramData\Microsoft\Crypto\PCPKSP\
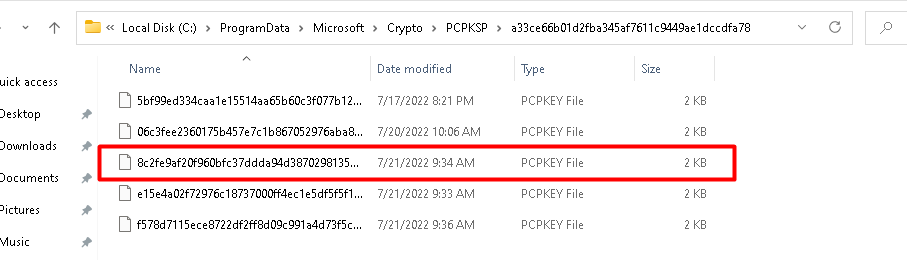
Let’s take a look at dsregcmd, and the Device Certificate after we repaired the certificate store with the command above
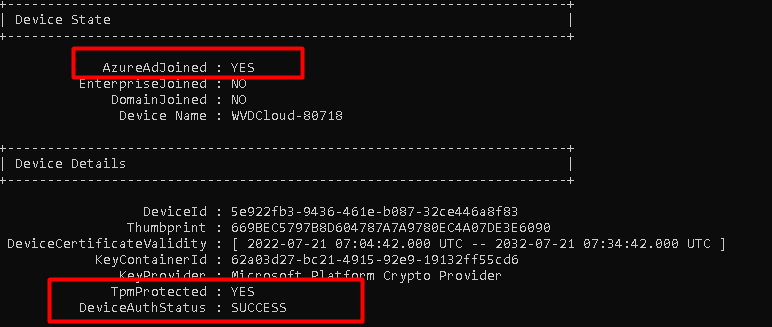
As shown above… the problem with the private key missing is fixed and everything is working again.
3. Importing the MS-Organization-Access certificate
Now we have seen what happens when removing and importing the MS-Organization-Access certificate on the same device let’s found out what happens when I export and import that MS-Organization-Access certificate on a device enrolled into another tenant.
I made sure I copied that cert to another device already enrolled into another tenant and removed the already present MS-Organization-Access certificate. You can guess what happens when you import the MS-Organization-Access certificate from a device enrolled in tenant a to a device enrolled in tenant b
Opening the CMD and looking at the output of dsregcmd /status will show you the same DeviceAUth error we noticed earlier. DeviceAuthStatus d009200b
But did you also notice the change in the TenantName? When removing the corresponding MS-Organization-Access certificate and importing one from another tenant, the device suddenly becomes Azure Ad Joined to another tenant! You can even log-in with a user from that specific tenant!
How the hell is that possible?
4. OIDS
We only imported the MS-Organization-Access certificate, right? So the Tenant Id Information NEEDS to be in the certificate! Let’s find out, shall we?
When looking at the Device certificate, you will need to start looking at the certificate details and to be specific we need to start looking at the Object Identifier (OID). An OID is nothing more than “a sequence of numbers in a format described by [RFC1778]. In many LDAP directory implementations, an OID is the standard internal representation of an attribute”
The representation of an attribute.…. sounds just like the thing we need, right?
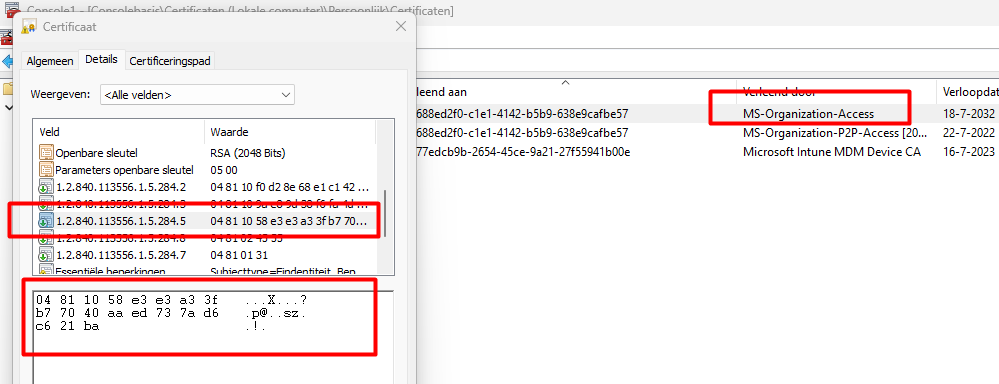
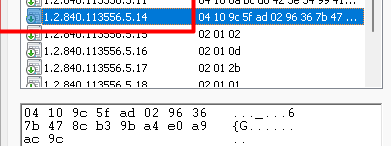
As shown above, when looking at the 1.2.840.113556.1.5.284.5 OID value in the MS-Organization-Access Certificate we can spot a nice scrambled DER encoded value!
First remove the 04(BITSTRING), 81 (the length of length in bytes), and 10 (the length of the data in bytes) The part that is left behind we can glue back together to get back our TenantID.
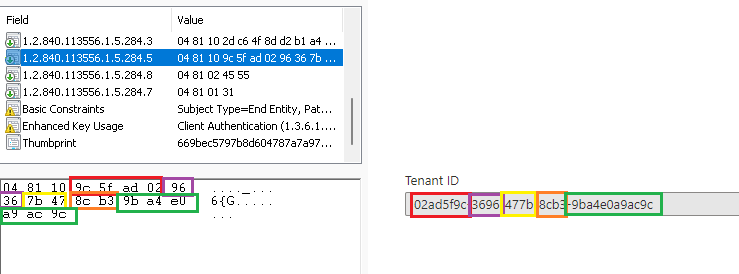
As shown above, the scrambled value is the actual Tenant ID. When looking at the MS-Organization-Access certificate we also could know if the device was Azure Ad Joined or Azure Ad registered. This one is a little bit easier to unscramble!
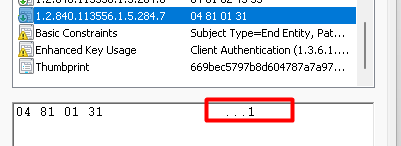
As shown above, the 1.2.840.113556.1.5.284.7 value is giving us the information we need to know if the device was Azure Ad Joined (1) or Azure Ad registered (0)
When running a Trace during the Azure Ad Join, we will notice that the process also uses this OID to determine the join status and the tenant id
Of course, the same goes for the Microsoft Intune MDM Device CA Certificate! The OID we need to check to determine the TenantID is 1.2.840.113556.5.14
With this information from these certificates, the device knows in which Tenant it’s Azure Ad Joined or AADR and in which Tenant it was MDM enrolled
5. Cleanup Intune Devices
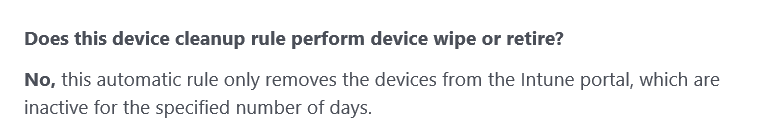
I guess most of us are using clean-up rules, right?
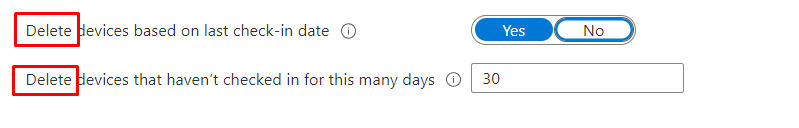
When you are using clean-up rules to keep your Intune environment nice and clean, and a device that hasn’t checked in for let’s say 30 days, it will be hidden from the Intune Portal not Deleted!! (even when the Intune Portal tells us otherwise!)
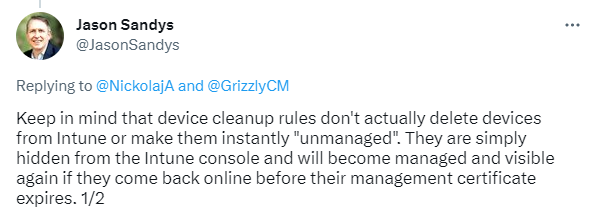
Without a deletion or retirement of the device, the Intune certificate will remain valid and will still be on the device. The Microsoft Intune MDM Device CA Certificate is the trust between your device and Intune, and as long as it doesn’t expire the device will make sure the Intune object will be brought “online” again. Only after 180 days when the Intune MDM device certificates have expired the device will be deleted by Intune
Conclusion
First of all, I want to thank Dr. Nestori Syynimaa (@DrAzureAD) / Twitter ! because his blogs are the real golden nuggets in this world!
I reached out to him yesterday evening but while writing down my question I already stumbled upon his blog! In his blog, he will show you way more details than I did! so go read it!
Secondly, knowing how stuff works is really really necessary! With this information, your troubleshooting skills will skyrocket and you will do better at your job!
What is "ms-organization-access" certificate why is it showing up in thycotic
I have been trying to fix an issue with our Thycotic Server for months now and can’t seem to find the help we have contacted both Microsoft and Thycotic support and both blame one another and me the customer never gets the problem solved. So I come to you Spiceheads before I just suggest we move to another password vault site.
Every time I connect to our Thycotic server I get a security prompt asking me to «Select a certificate to authenticate yourself to (site name)» and the certificate listed has a long alphanumeric string and the issuer is «ms-organization-access».
What is this certificate and how can I stop this from happening.
- local_offer Tagged Items
 Jordan (Thycotic)
Jordan (Thycotic)

Enter to win a Nespresso VertuoPlus
6 Replies

Gregory for Microsoft 
Brand Representative for Microsoft
Have you applied a 3rd party SSL cert to the SecretServer?

Yes we have set up and applied the SSL certificate and that works fine we get this pop-up in IE, edge, and Chrome but in firefox it’s fine. The prompts I’m getting are for client certificates, not the site SSL.

Jordan (Thycotic) 
Brand Representative for Delinea, Inc.
Hey, SSWK! Thank you for bringing this to my attention. Would you be able to send me a DM with your contact details? I’d love to get this over to our support team.
And I would wonder if in this case you have multiple certs for the same user account on this machine and therefore you’re being asked to pick when you authenticate to IIS over SSL.
I look forward to getting this solved for you shortly! 🙂

Thank you for your reply I have seen that article and we have no Group Policy set like that and its temporarily fixed by deleting the certificate from the personal store. I suspect its a IIS setting that is set by the installer or the device assigning the certificate is incorrectly set.

The issue has been found looks like the protocol handler Virtual directory was set to Ignore Client certificates and setting to Accept stopped the prompt.

Jordan (Thycotic) 
Brand Representative for Delinea, Inc.
SSWK wrote:
The issue has been found looks like the protocol handler Virtual directory was set to Ignore Client certificates and setting to Accept stopped the prompt.
AWESOME to hear! Sorry for all of the trouble you had to go through, but happy you were able to find a solution. Please send me a message if you have any questions or problems in the future. Best, Jordan
This topic has been locked by an administrator and is no longer open for commenting.
To continue this discussion, please ask a new question.
Read these next.
Snap! — Io, Feather Electricity, Smart Coops, Driverless Transport, Orionids
Your daily dose of tech news, in brief. Welcome to the Snap! Flashback: October 20, 1906: Dr. Lee DeForest announces his three-element electrical vacuum tube, later known as a triode (Read more HERE.) Bonus Flashback: October 20, 1970: So.
DISM error 14098 — Windows Server 2012 R2
Earlier this week, I assume a windows update failed and the next morning when my server boots, it redirects to the "Automatic Repair" screen. I've gone in and loaded the disk array drivers, and was able to access both the OS partition and the Data partit.
Pen Testing
Hey everyone, I'm looking to get Penetration testing in my budget for 2024. Has any of you had it done before? Do you have a company you'd use in the Atlanta ,GA area? We had it done about 5 years ago, but I'd like to try a new company if possible. Thanks.
Spark! Pro series – 20th October 2023
Happy Friday! I am off today, heading out for a weekend camping trip. The last one of the year. Have a great weekend and see you Monday. Just a reminder, if you are reading the Spark!, Spice it up. We like i.
Number of connections to this computer is limited — Local user login
Hi all,Came across this one today that I have never seen before when logging locally onto a domain joined Windows 10 machine — "The number of connections to this computer is limited and all connections are in use right now, Try conne.